Description
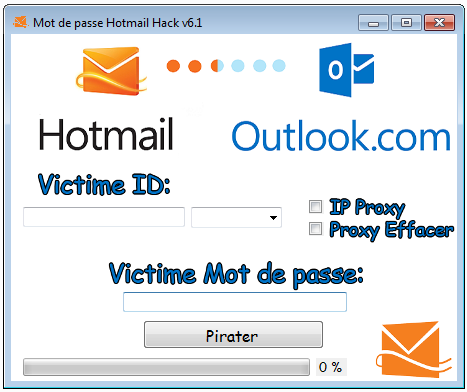
email hacker, mailbox hacker, email address hacker, email hacker, hacker email, email hacker, mailbox hack, hack an email
It all depends on the authentication system used.
If the target uses a one-factor authentication system, you will only need their password; however, if it is a two-factor system, you will also need to be in possession of the target's phone (which is not easy) to confirm the connection to the mailbox.
We have developed foolproof methods to successfully hack email accounts, including the use of a keylogger (keystroke recording program) which allows us to directly retrieve the login credentials of the targeted person as they type them on their keyboard.
To achieve our goals, we also use methods related to human psychology that lead the victim to share their information with us without suspecting anything (phishing). You can now spy on anyone without their knowledge and perhaps uncover unspeakable secrets and reap the benefits.




Reviews
There are no reviews yet.